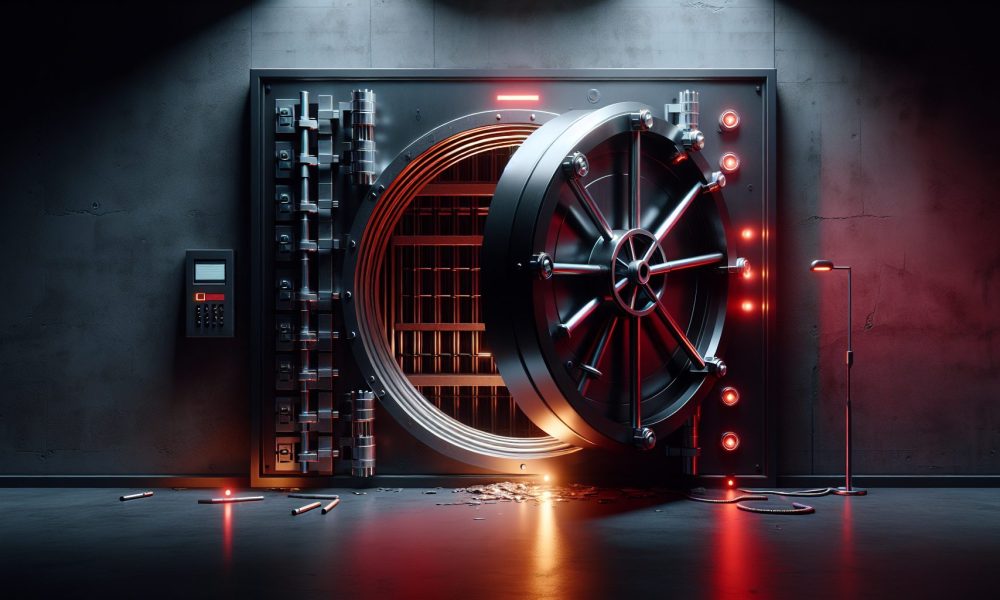
Venus Protocol Hack Drains $3.7M via Supply Cap Exploit
$3.7 million. Gone via supply cap manipulation. Venus Protocol detected the breach Sunday night. The venus protocol hack exploited liquidity pools for Thena (THE) and CAKE tokens using a two-phase attack that bypassed maximum supply limits.
Not ideal.
Venus paused all THE token borrows and withdrawals immediately. The platform’s risk manager, Allez Labs, traced the attack vector. Someone figured out how to weaponize supply caps. Classic DeFi vulnerability—code works until someone finds the edge case.
## How the Attack Unfolded
The exploiter executed this in two phases. First: accumulate 84% of THE token’s total market cap. Steady buying over time, no rush, no noise. Second: use that position as collateral to drain the protocol.
The haul: 6.67 million PancakeSwap CAKE tokens, 1.58 million USDC, 2,801 BNB, and 20 Bitcoin. Total value: $3.7 million according to Wu Blockchain.
The venus protocol hack followed a pattern I’ve seen before. Accumulation phase looks like organic buying. Nobody notices until the borrow phase starts. By then, too late.
Thena token crashed 17% to $0.2255 within 24 hours. Collateral liquidations accelerated the drop. Markets figured out what happened fast.
## The Supply Cap Vulnerability
Supply caps exist to prevent exactly this scenario. Maximum collateral limits per token protect against concentrated positions. The attacker found a bypass.
Allez Labs identified the mechanism: manipulate THE token liquidity to inflate borrowing power beyond intended limits. The protocol’s risk parameters didn’t account for this specific attack vector.
Venus halted withdrawals and borrowing for other low-liquidity tokens as a precaution. Smart move. If one token’s supply cap failed, others might share the vulnerability.
I’ve traded through DeFi summer 2020, the 2021 exploit wave, and every hack since. Supply cap attacks aren’t new. Compound saw similar issues in 2022. Cream Finance lost $130 million to the same pattern. Same vulnerability, different protocol.
## Broader Context: February Exploit Trends
The venus protocol hack stands out against February’s overall trend. Total crypto losses from hacks hit $49 million last month—lowest level in nearly a year, per blockchain security firm PeckShield.
But the threat shifted. Code exploits declined whilst phishing and social engineering scams surged. Hackers pivoted from protocol attacks to targeting individual users.
Nominis, a blockchain intelligence platform, noted most February attacks used phishing, malicious signatures, and address poisoning. Fake websites with nearly-identical domain names steal private keys. Users click one wrong link, funds vanish.
That pattern makes the Venus breach notable. Old-school DeFi exploit in an environment dominated by social engineering. The attacker went after protocol code, not user wallets.
## What Went Wrong
Venus Protocol operates on BNB Chain. Decentralized lending platforms rely on over-collateralization and liquidation mechanisms to stay solvent. Borrowers post collateral worth more than their loan. Price drops trigger liquidations.
Supply caps add another layer: maximum collateral per token type. Prevents whales from depositing illiquid tokens, borrowing liquid assets, then crashing the collateral price.
The attacker bypassed that safeguard. Accumulated 84% of THE tokens, deposited them as collateral, borrowed high-liquidity assets (CAKE, USDC, BNB, BTC), then exited.
Question is whether Venus can recover the funds. Most DeFi hacks don’t end in recovery. Poly Network got $600 million back in 2021 after the hacker returned it. Rare outcome. Usually, funds move through mixers and vanish.
## Protocol Response
Venus moved fast. Detected suspicious activity, paused affected markets, published details. Transparency matters when $3.7 million disappears.
Allez Labs, acting as risk manager, provided technical breakdown. The two-phase attack structure, collateral amounts, borrowed assets—all disclosed within hours.
Still investigating. The platform hasn’t announced whether it will compensate affected users or attempt fund recovery. Insurance funds exist on some DeFi protocols for exactly this scenario. Venus hasn’t clarified its position.
Cointelegraph reached out to Venus Protocol for comment. No response by publication time.
## Historical Precedent
Every DeFi cycle produces the same vulnerabilities. 2020: flash loan attacks. 2021: bridge exploits. 2022: oracle manipulation. 2023-2024: supply cap and liquidity manipulation.
The venus protocol hack fits the liquidity manipulation category. Accumulate low-float token, use as collateral, drain liquid assets. Cream Finance lost $130 million this way. Rari Capital lost $80 million. Hundred Finance lost $7 million.
Same attack, different protocols. The vulnerability persists because DeFi needs to support long-tail assets. Restrict collateral too much, you kill composability. Allow everything, you create attack vectors.
I’ve seen protocols solve this by implementing dynamic supply caps based on liquidity depth. Uniswap v3 uses concentrated liquidity to make manipulation expensive. Aave uses isolation mode for risky assets.
Venus apparently didn’t implement sufficient safeguards for THE token. The 84% accumulation should have triggered alerts. It didn’t.
## Market Impact
THE token down 17%. Not catastrophic compared to some exploit aftermath. Multichain’s MULTI token dropped 90% after its $126 million bridge hack. Mango Markets’ MNGO fell 50% after the $114 million exploit.
17% decline means market participants don’t expect total collapse. Either Venus absorbs the loss, or the damage stays contained to THE token holders.
Venus Protocol’s native token, XVS, will likely face pressure. Governance token holders often bear exploit costs through dilution or treasury depletion. Market will price that risk over coming days.
Borrowing rates for CAKE, USDC, BNB, and BTC on Venus probably spiked. $3.7 million exit reduced available liquidity. Supply-demand dynamics push rates higher when supply drops.
## What’s Next
Venus needs to close the supply cap vulnerability. Code audit, parameter adjustment, or fundamental redesign. Allez Labs will provide recommendations.
THE token borrowing and withdrawals stay paused until investigation concludes. Timeline unclear. Past DeFi exploits took 1-3 weeks to fully investigate and patch.
Low-liquidity token markets face extended restrictions. Venus can’t risk another attack vector whilst the first remains unresolved.
Broader DeFi ecosystem watches closely. Supply cap vulnerabilities affect multiple protocols. If Venus found a fix, others will implement it. If the vulnerability runs deeper, expect copycats targeting similar platforms.
Leverage kills. Every cycle proves it. This time, the leverage came from concentrated token positions bypassing supply limits.
All eyes on Venus Protocol’s next announcement.

 Bitcoin
Bitcoin  Ethereum
Ethereum  Tether
Tether  XRP
XRP  USDC
USDC  Solana
Solana  TRON
TRON  Lido Staked Ether
Lido Staked Ether  Cardano
Cardano  Avalanche
Avalanche  Toncoin
Toncoin